by PCS | Oct 29, 2025 | 2025, Tips & Tricks
Understanding both sides of cybersecurity is key: Offensive Security finds the cracks. Defensive Security seals them. Penetration Testing bridges the two, helping organizations stay one step ahead of attackers. #EthicalHacking #OffensiveSecurity #DefensiveSecurity...
by PCS | Oct 27, 2025 | 2025, Tips & Tricks
Strong audits rely on strong evidence. Audit evidence provides the facts, records, and insights auditors need to verify compliance and evaluate ISMS effectiveness. Whether qualitative or quantitative, every piece of evidence helps transform audit findings into trusted...
by PCS | Oct 24, 2025 | 2025, Tips & Tricks
Cyber threats don’t wait for software updates. That’s where virtual patching steps in, a proactive security layer that protects vulnerable systems even before official patches are released. It helps prevent exploits, maintain compliance, and secure legacy systems...
by PCS | Oct 23, 2025 | 2025, Updates
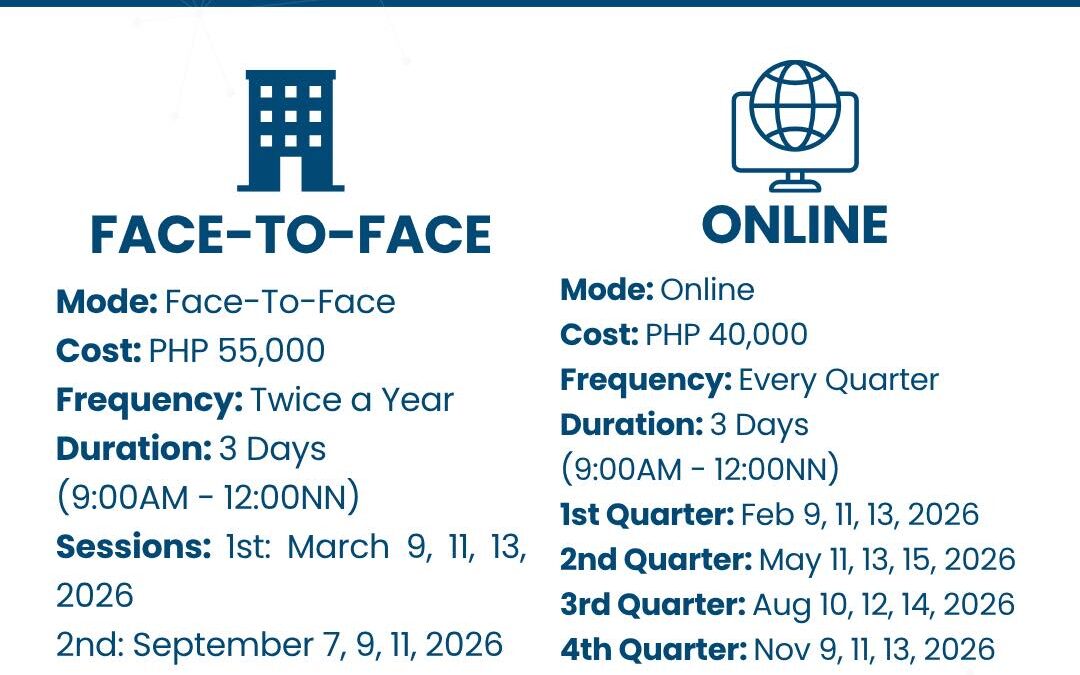
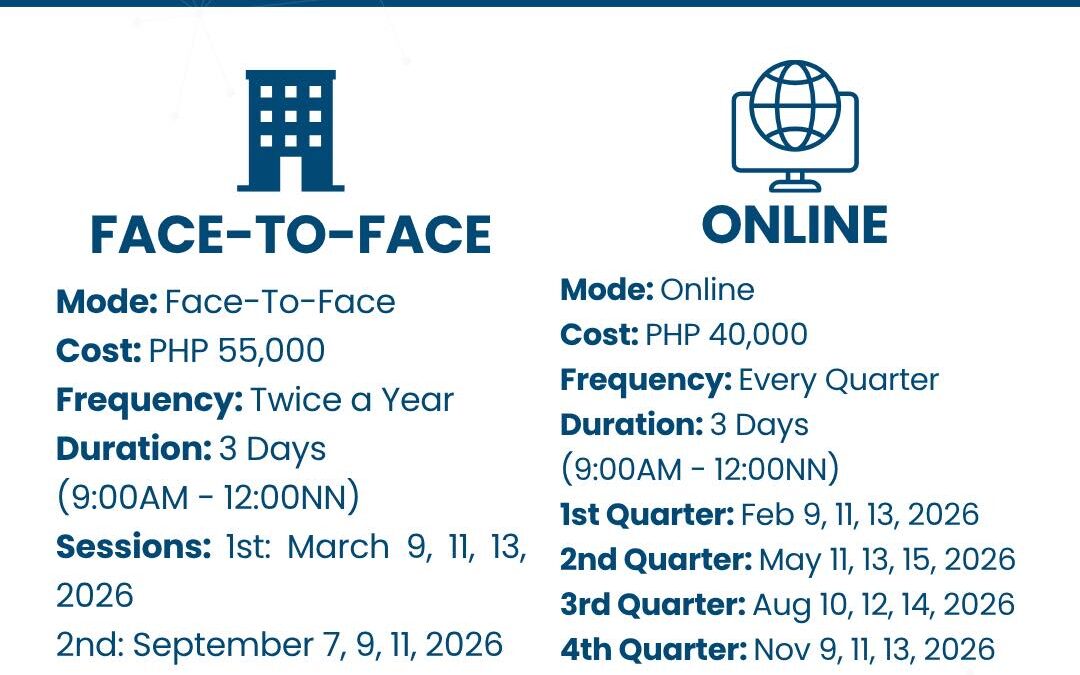
Plan Ahead for 2026! Our PECB ISO 27001 Lead Auditor Training with Certification is now open for both Face-to-Face and Online sessions next year. Email us: [email protected] #PinedaCyberSecurity #CyberSecurityMakesSenseHere #PECB #CyberTraining #ISMS...
by PCS | Oct 22, 2025 | 2025, Tips & Tricks
Frameworks and architectures are more than technical blueprints, they guide integration, ensure control, and help keep systems compliant as they evolve. Layering, modularization, and well-placed control points build resilient, secure infrastructures that align...