by PCS | Oct 9, 2025 | 2025, Tips & Tricks
Databases hold an organization’s most valuable data making them prime targets for cyber threats. From inference and injection attacks to web-based exploits, understanding these risks is key to strengthening your defense strategy. Secure your data, protect your...
by PCS | Oct 8, 2025 | 2025, Tips & Tricks
A well-structured recovery plan ensures resilience when incidents strike. From clear team roles to detailed recovery steps, preparation is key to minimizing downtime and restoring operations quickly. Effective recovery operations turn disruption into opportunity for...
by PCS | Oct 3, 2025 | 2025, Tips & Tricks
Think of Unified Threat Management (UTM) as your all-in-one guard dog for the network. Instead of juggling multiple tools, UTM streamlines protection with firewall, antivirus, and intrusion prevention in one system. Efficient, powerful, and built for today’s threats....
by PCS | Oct 2, 2025 | 2025, Tips & Tricks
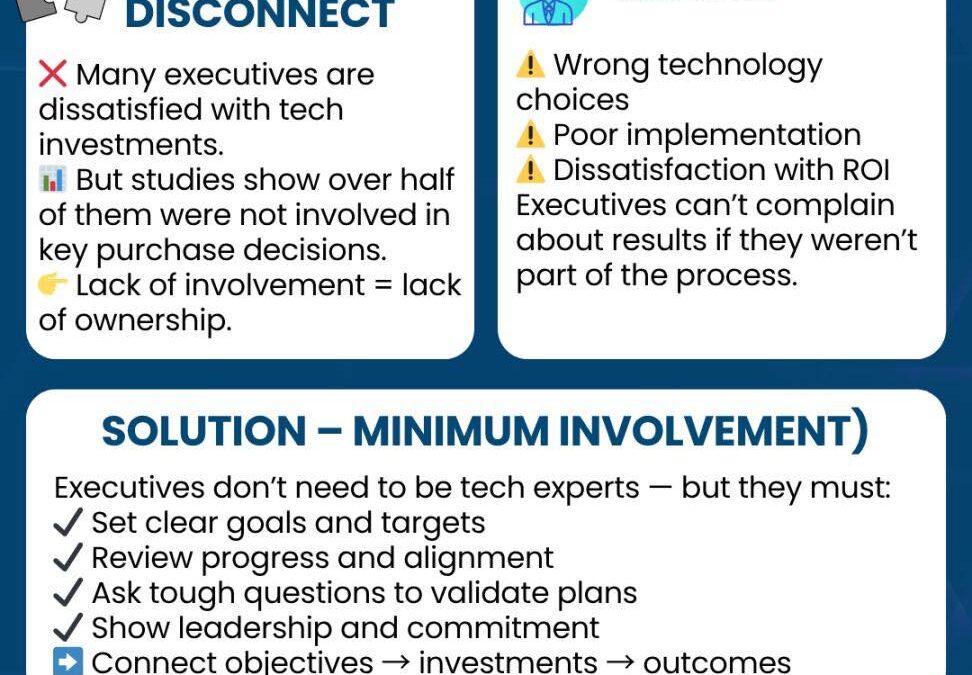
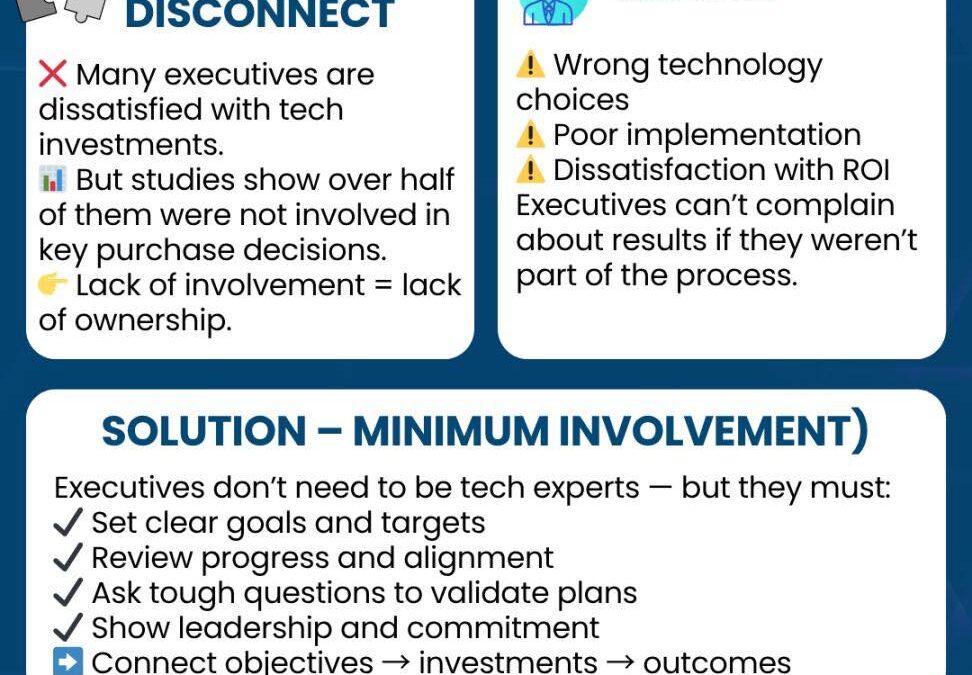
Executives often feel frustrated with technology outcomes—but many aren’t directly involved in making those decisions. True leadership doesn’t mean being a tech expert, but it does mean setting clear goals, asking the right questions, and showing commitment. Want...
by PCS | Sep 30, 2025 | 2025, Tips & Tricks
Daisy-chaining is a stepwise attack where an intruder links multiple small compromises to escalate access and reach a high-value target. Stay vigilant: enforce least privilege, monitor lateral movement, and train staff to spot social engineering attempts....