by PCS | May 20, 2025 | 2025, Tips & Tricks
Use IDS for visibility and analysis, and IPS for real-time defense. Many organizations deploy both to create a layered security strategy. #PinedaCyberSecurity #CyberSecurityMakesSenseHere #SecurityPlus #IDS #IPS #NetworkSecurity #IntrusionDetection #PCSCyberEd...
by PCS | May 19, 2025 | 2025, Tips & Tricks
AI isn’t replacing auditors, it’s empowering them with sharper tools to deliver faster, smarter, and more reliable audits. While AI significantly enhances audit quality, organizations must still consider: Financial investment Customization needs Trust and accuracy in...
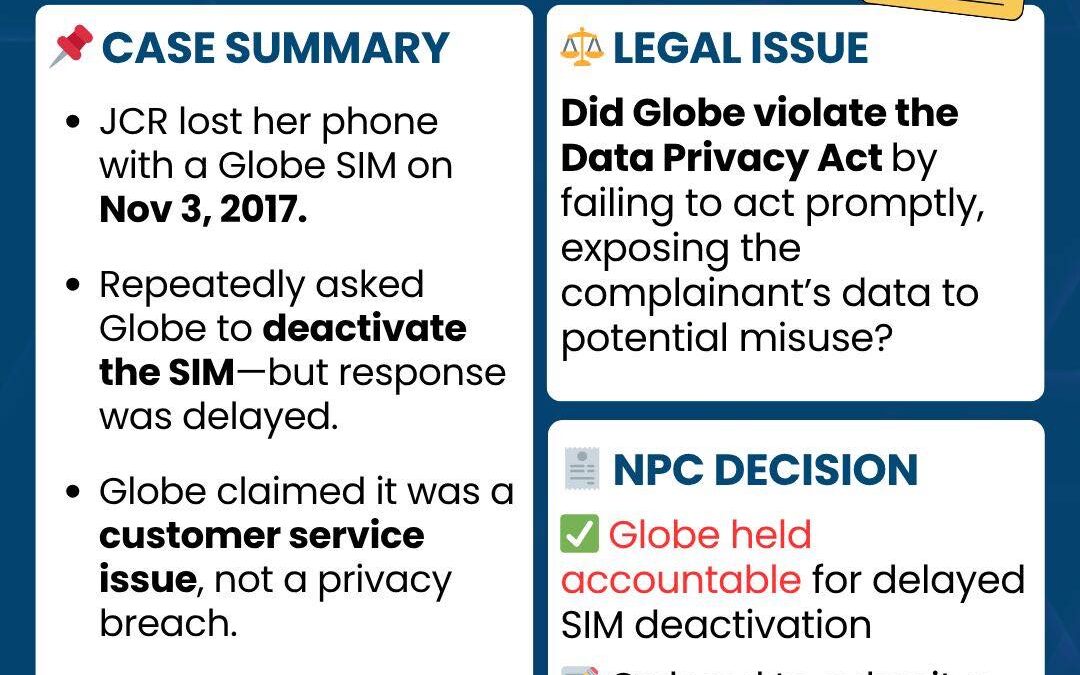
by PCS | May 16, 2025 | 2025, Tips & Tricks
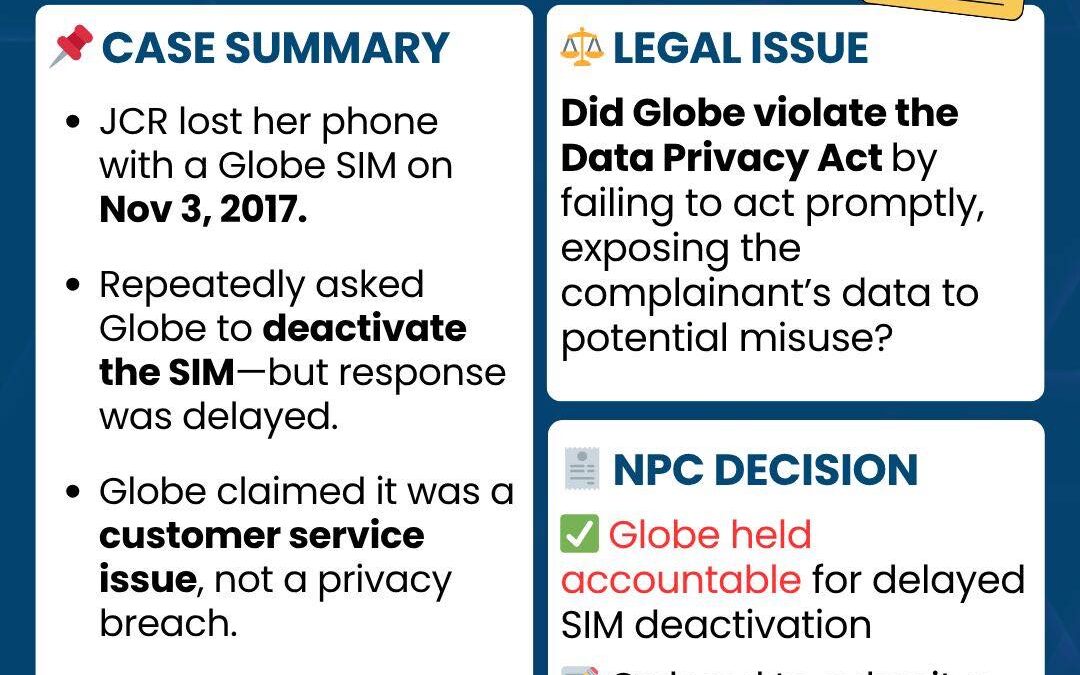
What starts as a simple service request can become a privacy risk. In JCR vs. Globe, the NPC ruled that inaction on lost SIMs can expose users to data threats. Telcos must treat SIM security as a data protection issue, not just customer support. #PinedaCyberSecurity...
by PCS | May 15, 2025 | 2025, Tips & Tricks
Privilege escalation is a high-impact threat. A single weak point can grant attackers full control. Combine proactive training, access controls, and detection tools to stay secure. #PinedaCyberSecurity #CyberSecurityMakesSenseHere #CISSP #PrivilegeEscalation #IAM...

by PCS | May 14, 2025 | 2025, Tips & Tricks
Incident management is the framework, and incident response is the action. You need both to keep your organization resilient and ready. #PinedaCyberSecurity #CyberSecurityMakesSenseHere #CISM #IncidentResponse #IncidentManagement #InfoSec #CyberPreparedness...
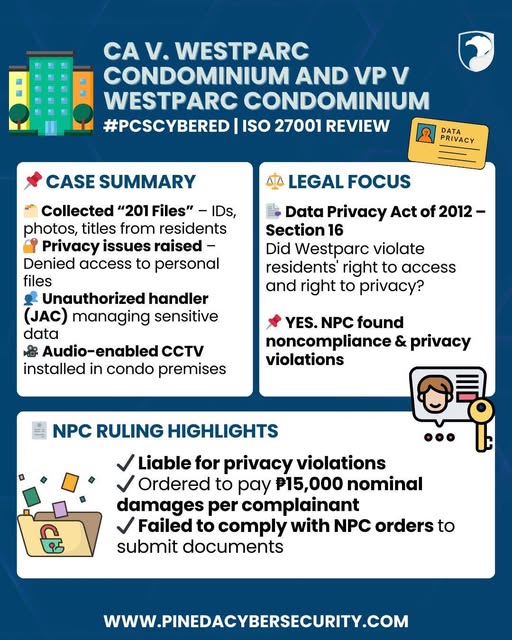
by PCS | May 9, 2025 | 2025, Tips & Tricks
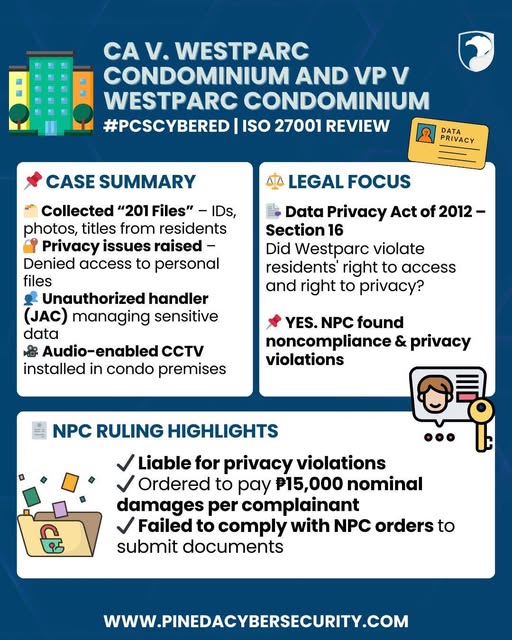
Data privacy is a right, it is not optional. Even routine data collection must have legal basis, safeguards, and transparency. Noncompliance, especially when ignoring regulator orders, has consequences. #PinedaCyberSecurity #CyberSecurityMakesSenseHere #NPC...