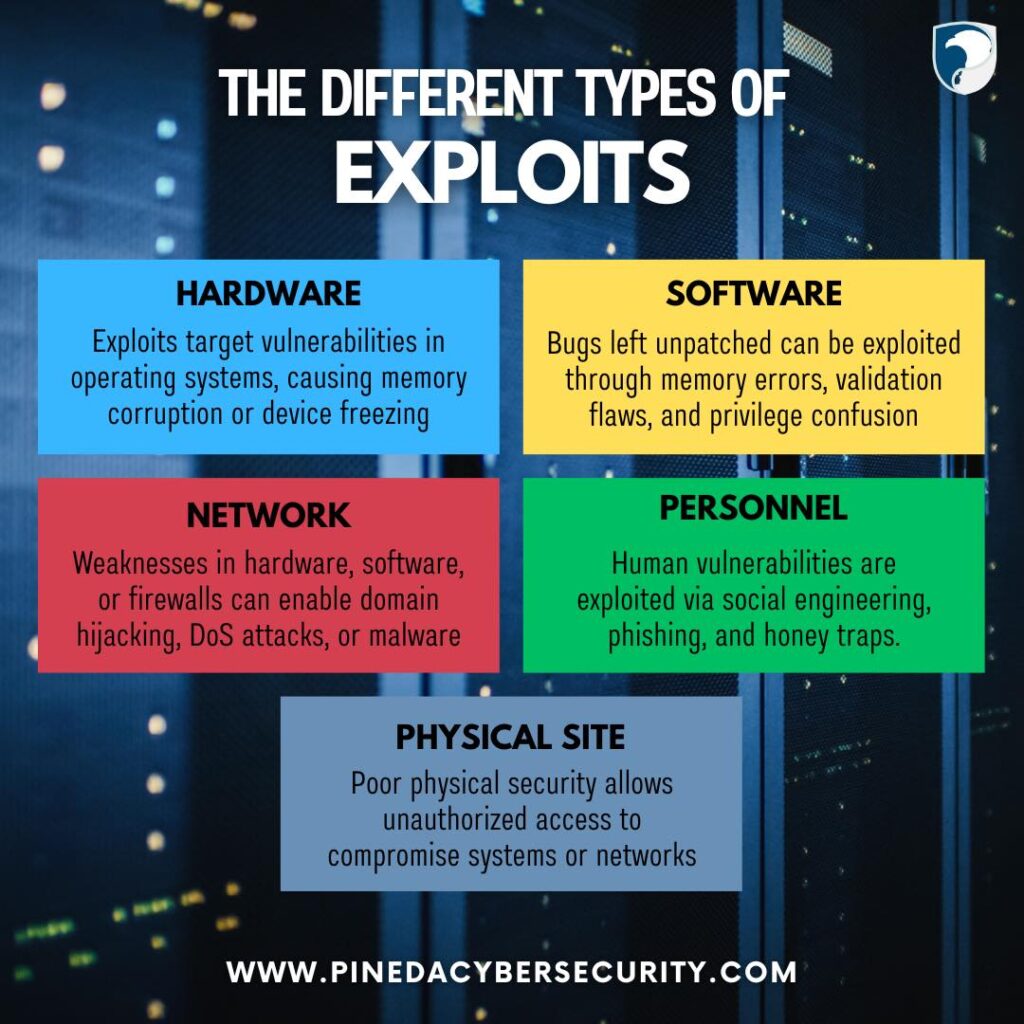
Understanding the different types of cyber exploits is the first step in safeguarding your organization. ![]()
From hardware vulnerabilities and software bugs to network gaps, personnel manipulation, and physical site breaches, cybercriminals are always on the lookout for entry points. ![]()
Strengthen your defenses by identifying weak spots and implementing robust security measures like regular patching, training, and access controls.
#CyberSecurity #PinedaCyberSecurity #CyberSecurityMakesSenseHere #CyberThreats #DataProtection #NetworkSecurity #PhysicalSecurity #OnlineSafety #CyberAwareness #SecureYourBusiness