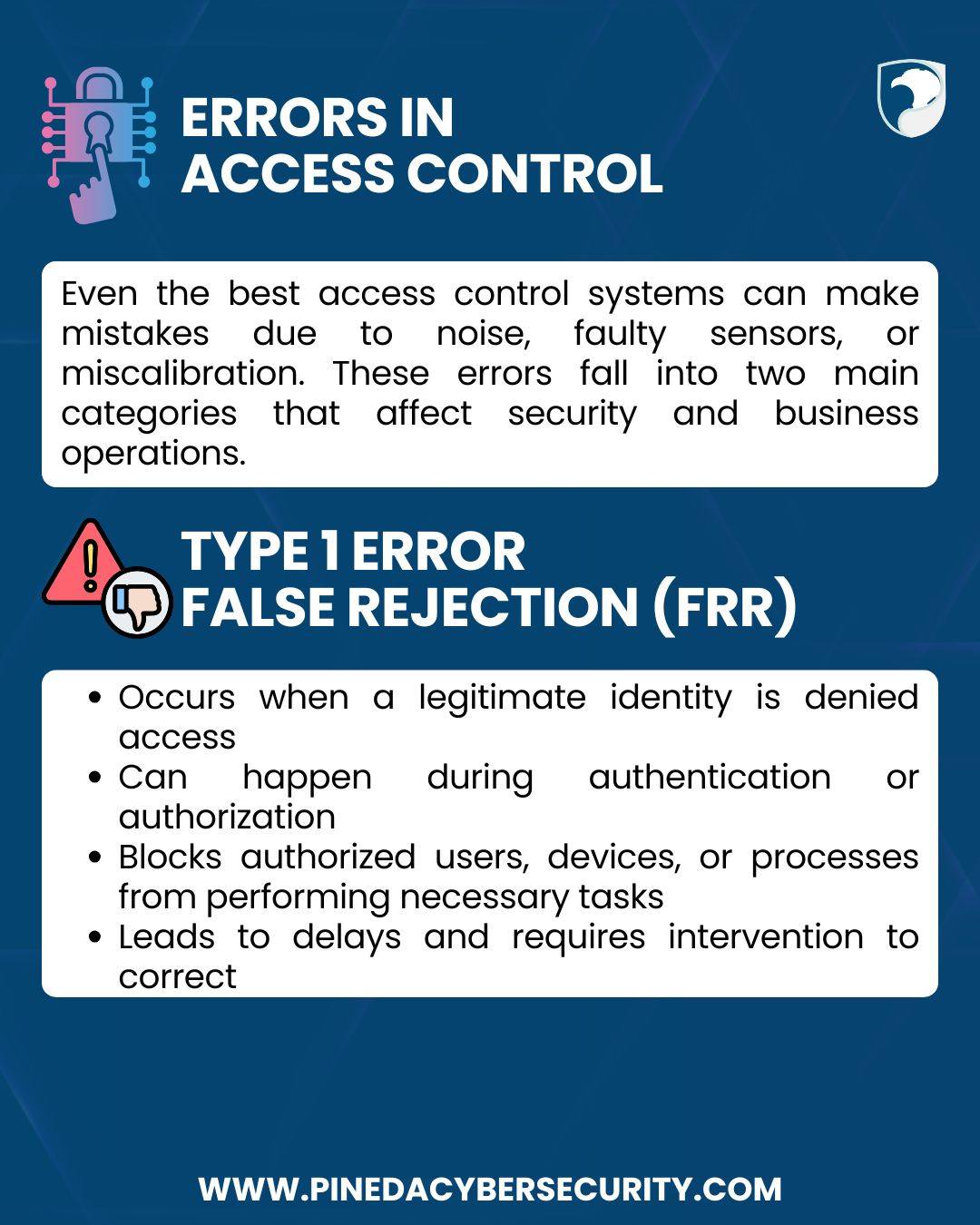
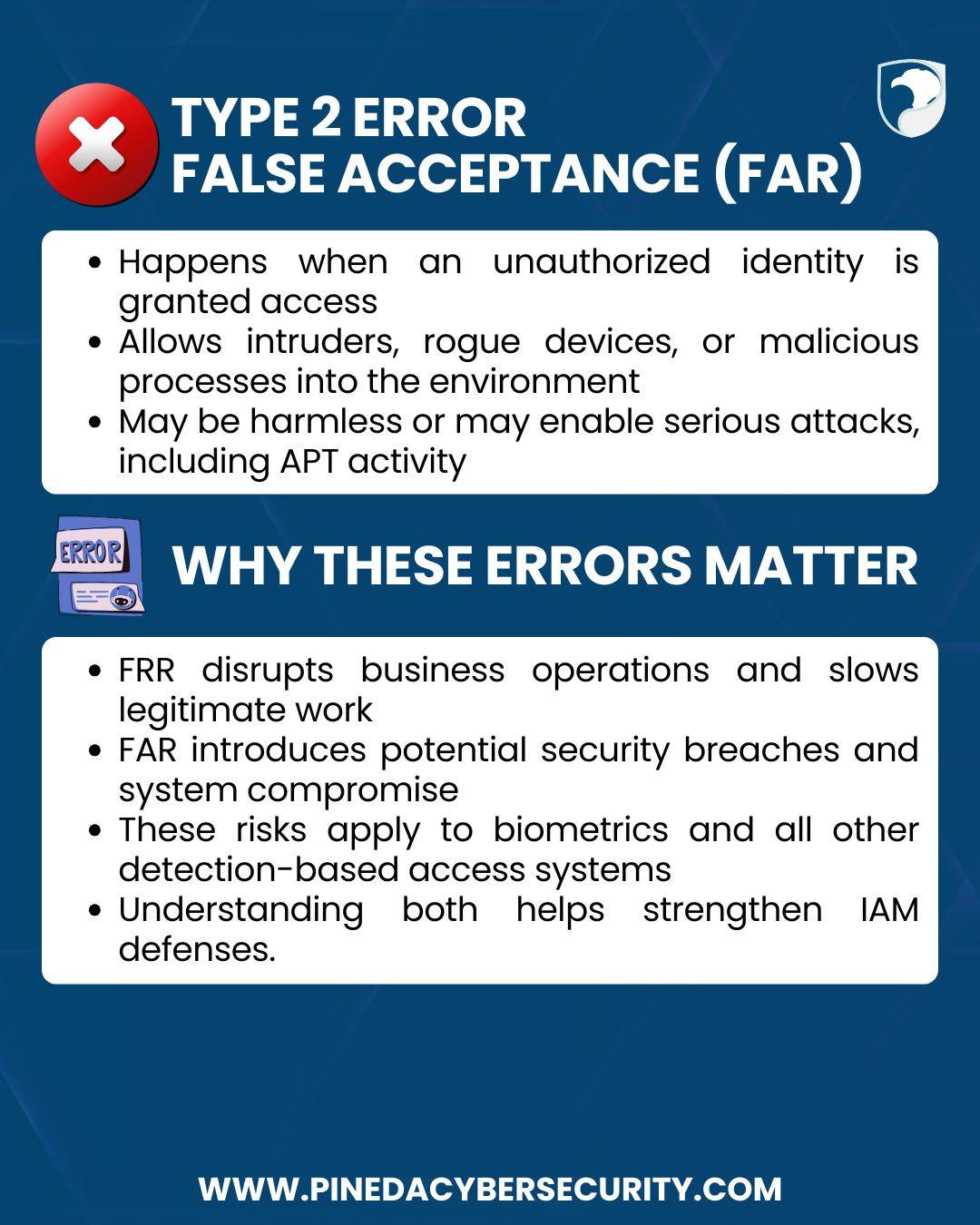
Errors in access control happen even in well-designed IAM environments. False rejections disrupt legitimate work, while false acceptances can open the door to unauthorized activity—even serious threats.
By understanding these error types, security teams can fine-tune controls, reduce disruptions, and strengthen overall protection across biometric and non-biometric systems.
#InformationSecurity #RiskManagement #Authentication #Authorization #PinedaCybersecurity #CyberSecurityMakesSenseHere