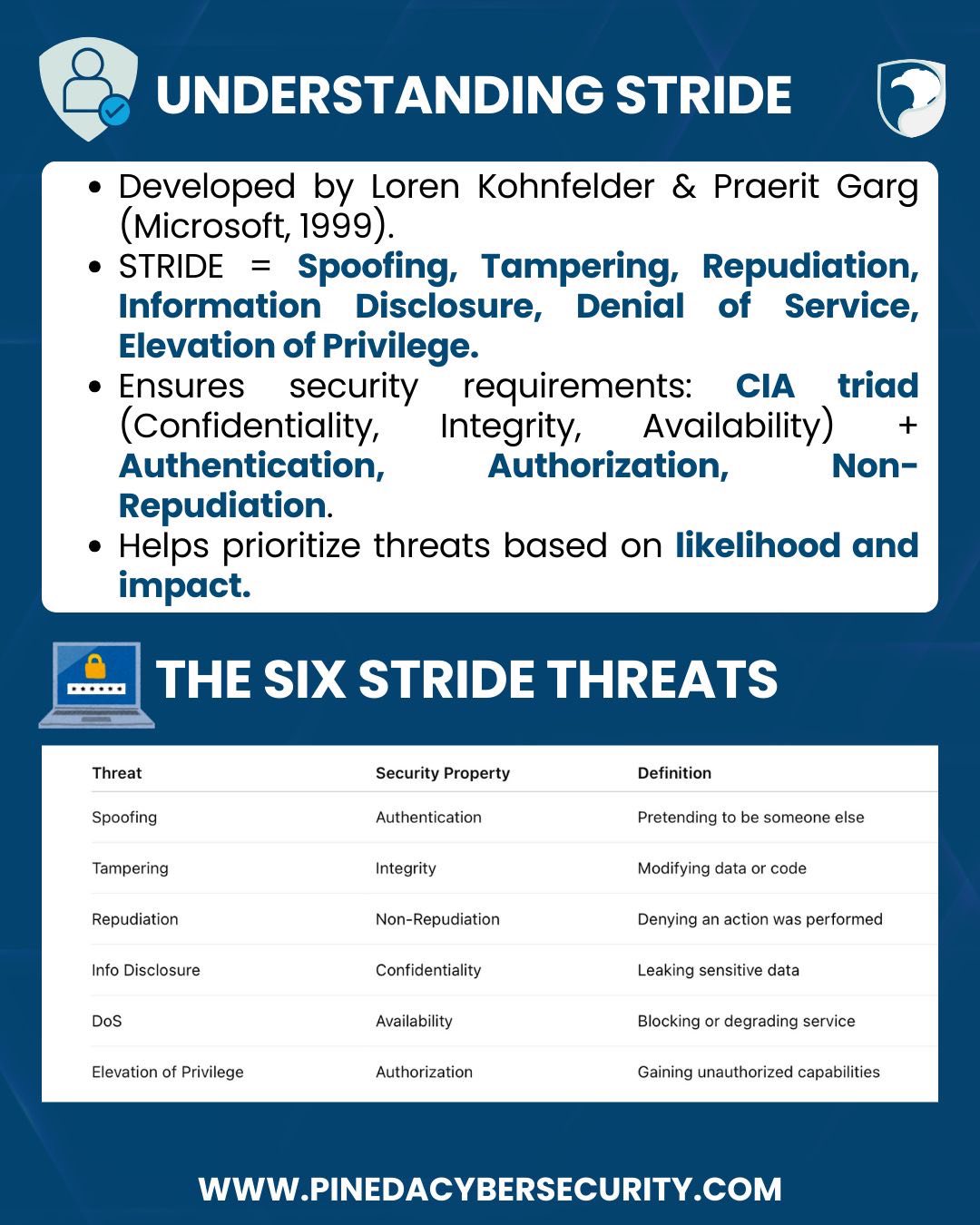
Today’s focus is STRIDE Threat Modeling Methodology, one of the oldest and most widely used ways to identify vulnerabilities in systems.
By breaking threats into six categories, namely Spoofing, Tampering, Repudiation, Information Disclosure, Denial of Service, and Elevation of Privilege, STRIDE helps organizations understand risks, prioritize countermeasures, and protect critical assets.
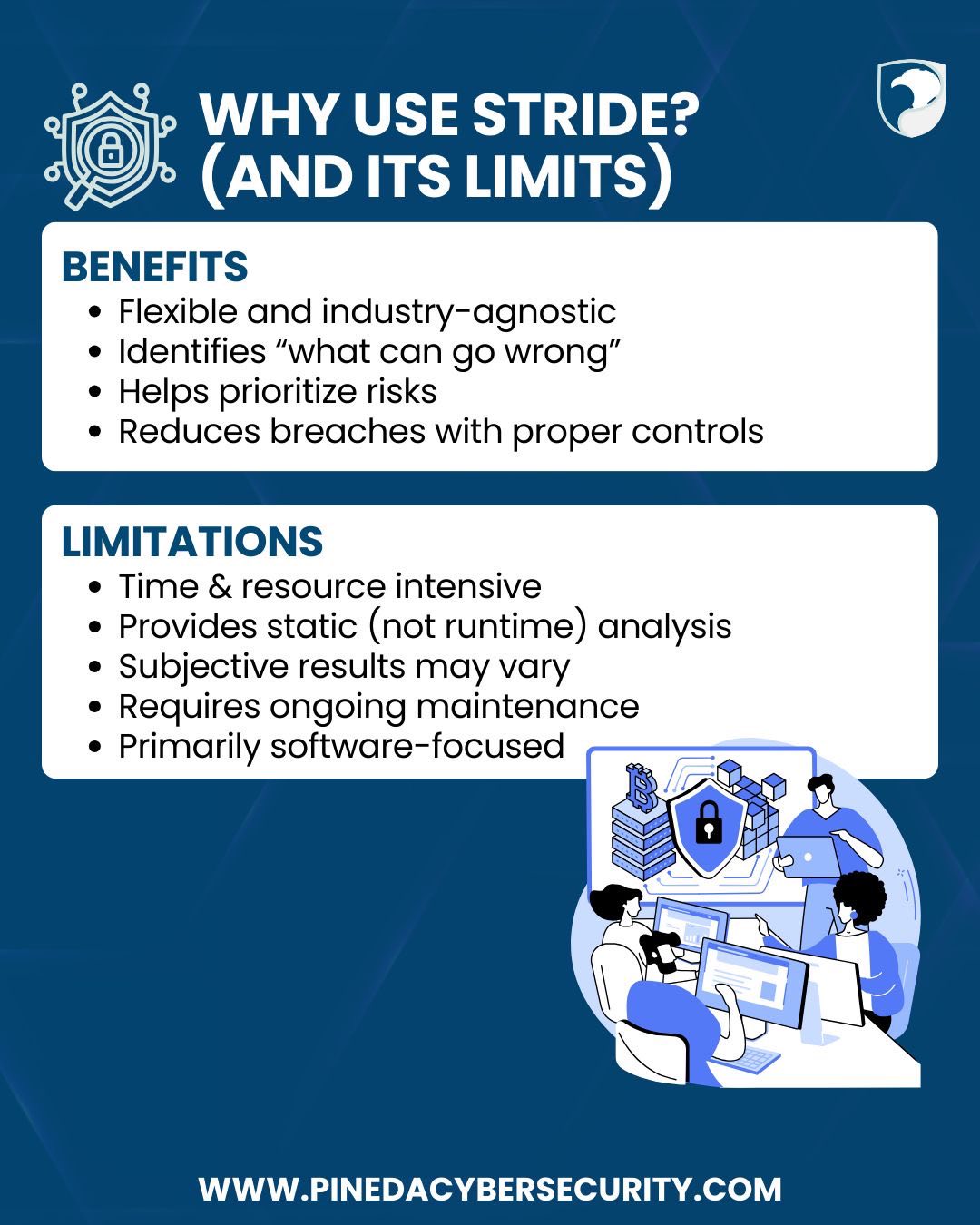
It’s flexible, powerful, and effective, but it requires expertise, resources, and continuous maintenance.
#PinedaCybersecurity #CyberSecurityMakesSenseHere #PCSCyberEd #CISSPReview #ThreatModeling #STRIDE #InfoSec #CyberAwareness #SecurityTesting #VulnerabilityManagement